Experience Safer Connections Using A Fast SOCKS5 Proxy For Browsing
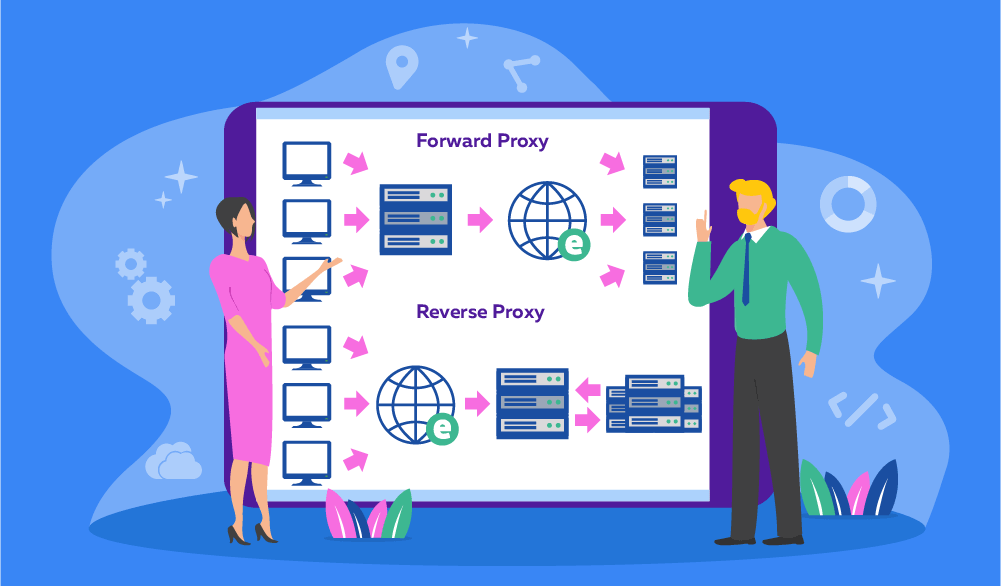
In today’s digitally connected world, privacy and speed are two of the most essential components of a safe and satisfying internet experience. Whether you’re working remotely, streaming content, or simply browsing your favorite websites, ensuring your data is secure and your connection is stable is more important than ever. One of the most effective and reliable tools for achieving this balance is a SOCKS5 proxy. Fast, flexible, and incredibly secure, a SOCKS5 proxy is the perfect solution for users who want to enjoy safer connections without compromising on speed or performance. A SOCKS5 proxy serves as an intermediary between your device and the internet, routing your online traffic through a proxy server. This setup masks your IP address and helps protect your identity, making it significantly harder for websites, advertisers, or cybercriminals to track your online activities. Unlike older proxy protocols, SOCKS5 supports both TCP and UDP connections, which allows for smoother and faster performance especially beneficial for tasks like streaming, gaming, and peer-to-peer file sharing. Its enhanced flexibility makes it ideal for modern users seeking both privacy and speed.
For users looking for reliable and high-quality proxies, look out those proxies I found On Bookipi a few days ago. They offer excellent services that cater to both security and performance, ensuring your connection remains swift while safeguarding your data. By using such fast proxies, you’ll enhance your browsing experience, minimizing delays and maximizing protection. What truly sets a SOCKS5 proxy apart is its superior performance. It handles fewer errors and uses less bandwidth compared to many other proxy types. This means you experience fewer interruptions, faster loading times, and a more reliable connection overall. Whether you’re accessing geo-restricted content, managing multiple social media accounts, or conducting sensitive business transactions, a fast SOCKS5 proxy ensures that your data flows securely and swiftly across the internet. Another key advantage of using a SOCKS5 proxy is its compatibility with a wide range of applications. From browsers and torrent clients to remote desktop tools and messaging platforms, SOCKS5 can be integrated seamlessly to provide enhanced protection and performance.
This versatility empowers users to customize their privacy settings across multiple tools and devices, creating a unified and secure browsing environment. Furthermore, many SOCKS5 proxies now come with added features such as encryption, multi-layered security, and no-log policies. These enhancements not only increase safety but also give users peace of mind knowing their information is protected from surveillance and unauthorized access. For individuals and businesses alike, this can be a game-changer in protecting sensitive information and maintaining confidentiality in online interactions. In conclusion, experiencing safer connections with a fast SOCKS5 proxy is not just a smart move it is a vital step toward better digital well-being. It combines the best of both worlds – robust security and impressive speed. Whether you’re an everyday internet user or a tech-savvy professional, incorporating a SOCKS5 proxy into your online routine can significantly enhance your browsing experience. With growing concerns around online privacy, now is the perfect time to embrace this powerful tool and take control of your digital safety in a fast, reliable, and positive way.
![OnlyMP3.to - The Free YouTube to MP3 Converter [320 kbps]](https://www.startertutorials.com/blog/wp-content/uploads/2024/06/Youtube_to_MP3_Converter_Onlymp3.to_-1024x576.jpg)